Shavlik is dedicated to significantly reducing from months to minutes the time-to-value for IT professionals.
Proven, reliable on-premise and cloud-based Shavlik technologies enable customers to manage both physical and virtual machines, deploy software, discover assets, simplify configuration, and ensure endpoint security. By delivering to organizations of all sizes and types the sophisticated capabilities enjoyed by large enterprises, Shavlik is driving the democratization of IT.
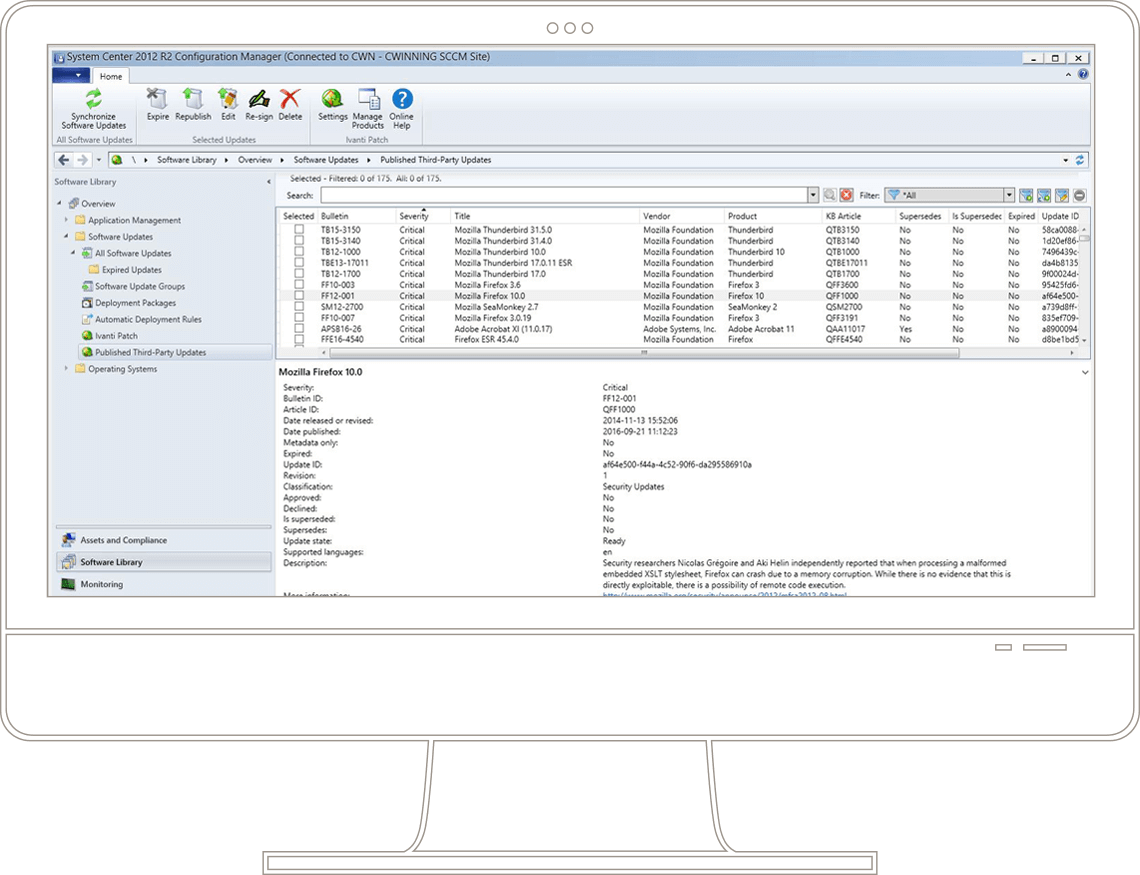
In April 2013, LANDESK acquired VMware’s Protect product family of IT management solutions, which VMware acquired through its purchase of Shavlik Technologies in 2011. In January 2017, as a result of the purchase of LANDESK by Clearlake Capital and the establishment of the new company Ivanti, both the Shavlik and LANDESK product brands were woven into the Ivanti line of solutions.